

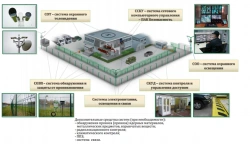
Designed to detect information security incidents, including those with signs of computer incidents, through the collection, normalisation, long-term storage, correlation search and analysis of information security events.


















Tell us what you need and get quotes from verified suppliers